Security Services Customized
HTG can help you at every phase as you mature your company’s security state. If you have a plan but have uncertainty about current compliance or relevance, let HTG help you identify any and all potential gaps. Perhaps you don’t have a security plan at all. If not, we can help you develop a customized set of standards and processes tailored specifically to your company’s unique requirements. You may have a strong IT department but you feel you’re lacking in security guidance. Regardless of your security state, HTG customizes security services to seamlessly move your business to the next level at your pace.

Free Security Webinar!
Engage with HTG’s security expert and resident CISO (Chief Information Security Officer) Jim Foote, as he covers a wide variety of C-Suite level security topics.
Sobering Facts
Statistics demonstrate that it usually takes 18 months to recover from a data breach. Typically, companies are unable to sustain that loss over this critical 18 month period and 60% actually go out of business. The average cost of a breach in 2016 was $4 million or $158 per record. For healthcare data, the numbers escalate to $355 per record. (US National Cyber Security Alliance). Read More about this year’s security breaches and their costly settlements.
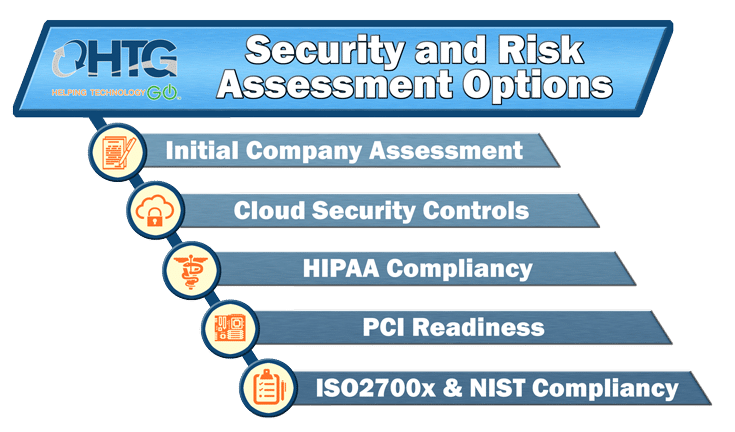
Risk Assessment & Risk Management
Those are the facts and you’ve likely heard them before but where to start to ensure the most comprehensive security protocols are in place? The key to combating increasingly creative cyber threats is to engage one of our CISO a to . . .
- analyze risks
- secure the business
- provide sound security advice and training
- collaborate to build a comprehensive company-wide security strategy, and
- ensure regulatory compliance . . .
. . . and that’s exactly what our Virtual CISO Advisors do but at a fraction of the cost of a full-time C-level executive.
Consider This: When an employee’s laptop was stolen from a parked vehicle outside of the workforce member’s home it resulted in a 2.5 million dollar fine because the health organization employer, CardioNet had
- “insufficient risk analysis and risk management processes in place at the time of the theft”;
- drafted policies and procedures, but not implemented them;
- no final documentation for implementing safeguards for ePHI; and
- no policies and procedures for mobile device security.
Two Words – Reasonable and Appropriate
In a nutshell, whatever is considered “reasonable and appropriate” summarizes the standard that NIST, FTC, HIPAA and FISM agencies use for measuring compliance in a company audit or analysis. But what exactly does that mean? Do you know if you have implemented security standards, process, and policies that “reasonably and appropriately”meet the varied requirements set forth by a plethora of regulatory entities?
Remember, your brand, reputation and information assets are at stake. And without people and process in place, whatever technology you have falls flat.
Call HTG Now for an Independent Assessment to meet today’s constantly ever changing cyber threats.
Take this one minute Security Risk Self-Assessment test
and instantly see your results:
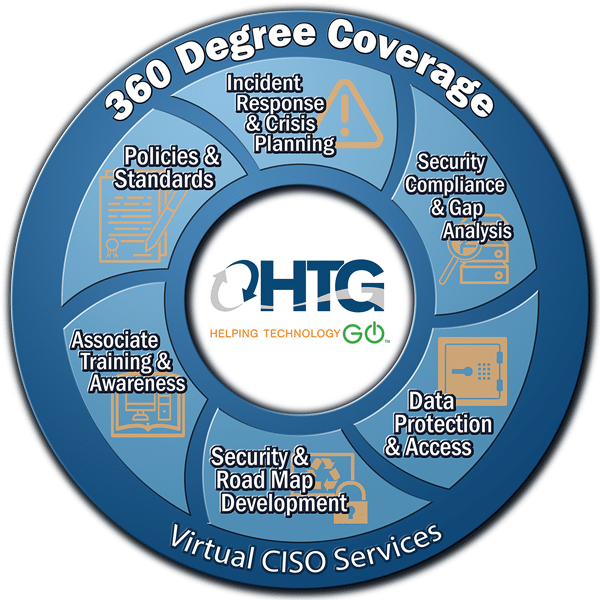
Virtual CISO Services
Every company needs security but many executives don’t know where to start and have concerns that building a comprehensive security strategy would be cost-prohibitive.The solution? HTG’s Virtual CISO. At half the cost of a full-time Chief Security Officer, HTG’s Virtual CISO Advisors provide weekly invaluable C-Suite security guidance on a schedule determined by the client. Whether your needs are security/data breach education/training, policy/process development, incidence response teaming, ensuring regulatory compliance, or all of the above, the convenience and cost saving benefits of a Virtual CISO are indisputable.
Small and Mid-Sized Companies – Special Alert –
The US Security and Exchange Commission warned there is a “need for greater focus on the cyber security challenges facing small and mid-size businesses.” The reality is the majority of the cyber attacks last year were directed at small and mid-sized companies. Why? Because they are often times easier targets. Large companies have the capacity to put sophisticated security teams in place, but small and mid-sized companies lack the required security or controls. The fact is, cyber criminals are interested in quick, easy data to sell for quick easy money.
Regardless of your business size, the time to act is now. The most common mistake is waiting until a security crisis or data breach occurs to build a plan. With the convenient, cost-saving expertise of a Virtual CISO at-the-ready, you can have comprehensive policies and process in place when it matters most. Get a better night’s sleep with the confidence that you and your teams know how to prevent, respond to, or mitigate the loss of reputation, career, critical data, finances, proprietary assets . . . and more.
